Endpoint Detection and Response (EDR) in Cyber Essentials
Endpoint Detection and Response (EDR), also known as Endpoint Detection and Threat Response (EDTR) is a security solution which monitors end-user devices, such as laptops or mobile phones, and can also be applied to servers to proactively detect and react to cyber threats such as ransomware and malware.
What is an Endpoint?
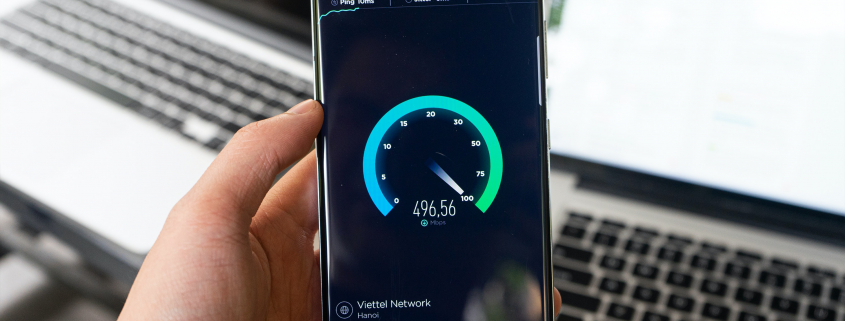
An endpoint is anything at the end of a network cable or Wi-Fi connection. This could be the laptops or computers used by your workforce, business and personal mobile phones, tablets, servers and anything in the virtual environment. Traditionally, antivirus software has been used to stop viruses and malware on your devices. As technology has progressed and hackers have increased their knowledge, it’s more important than ever to ensure that all of your endpoint devices are considered when planning cyber security.
Read more